Hi
This does not seem to work. I do not see any multi tenancy selector when logged in to kibana.
Is there anything else that needs to be configured?
OS: Windows Server 2016
ELK version: 7.2.0
ROR Elasticsearch: readonlyrest-1.18.4_es7.2.0
ROR Kibana: readonlyrest_kbn_enterprise-1.18.5-pre13_es7.2.0
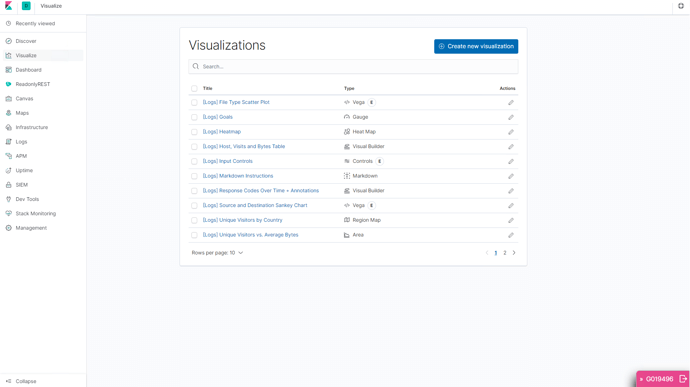
Screenshot from kibana
Elasticsearch log allowed request
[2019-08-26T11:03:35,297][INFO ][t.b.r.a.l.AclLoggingDecorator] [U-114-270-028-ROR] ALLOWED by { name: '::ADMIN_BP::', p
olicy: ALLOW, rules: [jwt_auth,kibana_access,indices] req={ ID:1166174822-738288830#2047, TYP:GetIndexTemplatesRequest
, CGR:Role_kibana_admin_blueprism, USR:G019496, BRS:false, KDX:null, ACT:indices:admin/template/get, OA:172.16.111
.87/32, XFF:x-forwarded-for=139.113.87.153, DA:172.16.111.87/32, IDX:<N/A>, MET:GET, PTH:/_template?pretty, CNT:<N
/A>, HDR:Connection=close, content-length=0, host=u-114-270-028:9210, jwt=Bearer <MY TOKEN>, x-forwarded-for=1
39.113.87.153, x-forwarded-host=139.113.87.153:5610, x-forwarded-port=55346, x-forwarded-proto=http, x-ror-current-group
=Role_kibana_admin_blueprism, x-ror-kibana-request-method=post, x-ror-kibana-request-path=/api/console/proxy, HIS:[::TE
ST::-> RULES:[auth_key->false], RESOLVED:[group=Role_kibana_admin_blueprism]], [::LOGSTASH::-> RULES:[auth_key_sha256->f
alse], RESOLVED:[group=Role_kibana_admin_blueprism]], [::KIBANA-SRV::-> RULES:[auth_key_sha256->false], RESOLVED:[group=
Role_kibana_admin_blueprism]], [::ADMIN_BP::-> RULES:[jwt_auth->true, kibana_access->true, indices->true], RESOLVED:[use
r=G019496;group=Role_kibana_admin_blueprism;av_groups=Role_kibana_admin_blueprism;response_hdr=x-ror-kibana_access=admin
]] }
readonlyrest.yml
readonlyrest:
access_control_rules:
- name: "::LOGSTASH::"
auth_key_sha256: <MY LOGSTASH CREDENTIALS>
actions: ["indices:data/read/*","indices:data/write/*","indices:admin/template/*","indices:admin/create"]
indices: ["queueitems-*", "sessions-*", "resources-*", "queues-*"]
- name: "::KIBANA-SRV::"
auth_key_sha256: <MY KIBANA CREDENTIALS>
verbosity: error
- name: "::ADMIN_BP::"
indices: ["queueitems-*", "sessions-*", "resources-*", "queues-*", ".kibana", ".monitoring*", ".reporting*", ".tasks*", ".kibana_task*",".readonlyrest", "kibana_sample*"]
kibana_access: admin
jwt_auth:
name: "webseal"
roles: ["Role_kibana_admin_blueprism"]
- name: "::RW_BP::"
kibana_access: rw
indices: ["queueitems-*", "sessions-*", "resources-*", "queues-*", ".kibana", ".monitoring*", ".reporting*", ".tasks*", ".kibana_task*", "kibana_sample*"]
kibana_hide_apps: ["readonlyrest_kbn"]
jwt_auth:
name: "webseal"
roles: ["Role_kibana_readwrite_blueprism"]
- name: "::RW_BP (personal)::"
kibana_access: rw
indices: ["queueitems-*", "sessions-*", "resources-*", "queues-*", ".kibana_personal_bp_@{user}", ".monitoring*", ".reporting*", ".tasks*", ".kibana_task*","@{user}-*", "kibana_sample*"]
kibana_index: ".kibana_personal_bp_@{user}"
kibana_hide_apps: ["readonlyrest_kbn"]
jwt_auth:
name: "webseal"
roles: ["Role_kibana_readwrite_blueprism", "Role_kibana_admin_blueprism"]
- name: "::RO_BP::"
kibana_access: ro
indices: ["queueitems-*", "sessions-*", "resources-*", "queues-*", ".kibana", "kibana_sample*"]
kibana_hide_apps: ["readonlyrest_kbn", "kibana:visualize", "canvas", "apps", "ml", "infra:infrastructure","infra:logs", "apm", "uptime", "siem", "kibana:dev_tools", "monitoring", "kibana:management"]
jwt_auth:
name: "webseal"
roles: ["Role_kibana_readonly_blueprism"]
jwt:
- name: webseal
signature_algo: RSA
signature_key: "<MY PUBLIC KEY>"
user_claim: sub
roles_claim: groups
header_name: jwt
elasticsearch.yml
cluster.name: rortest
node.name: U-114-270-028-ROR
network.host: U-114-270-028
http.port: 9210
transport.port: 9538
xpack.security.enabled: false
discovery.zen.ping.unicast.hosts: ["U-114-270-028"]
cluster.initial_master_nodes:
- U-114-270-028-ROR
kibana.yml
server.port: 5610
server.host: "localhost"
server.basePath: "/kibana"
server.rewriteBasePath: false
elasticsearch.hosts: "http://U-114-270-028:9210"
xpack.graph.enabled: false
xpack.ml.enabled: false
xpack.monitoring.enabled: true
xpack.security.enabled: false
xpack.watcher.enabled: false
readonlyrest_kbn.forward_auth_header: jwt
elasticsearch.requestHeadersWhitelist: [jwt]
#readonlyrest_kbn.jwt_query_param: "jwt"
#Real username and password stored in keystore. For reference https://www.elastic.co/guide/en/kibana/current/secure-settings.html
#elasticsearch.username: "kibana"
#elasticsearch.password: "kibana"
readonlyrest_kbn.clearSessionOnEvents: ["never"]
Decoded JWT
{
"sub": "G019496",
"iss": "https://www.example.com",
"aud": "urn:liberty",
"iat": 1566801867,
"exp": 1566805467,
"sess": "f2cdaec0-c7cc-11e9-a8b8-005056824880",
"groups": [
"Role_kibana_admin_blueprism",
"not_relevant_role_1",
"not_relevant_roles_2",
"not_relevant_roles_3",
"not_relevant_roles_4",
"not_relevant_roles_5",
"not_relevant_roles_6",
"not_relevant_roles_7",
"not_relevant_roles_8",
"not_relevant_roles_9",
"not_relevant_roles_10",
"not_relevant_roles_11",
"not_relevant_roles_12"
]
}