Hello
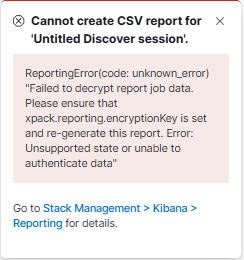
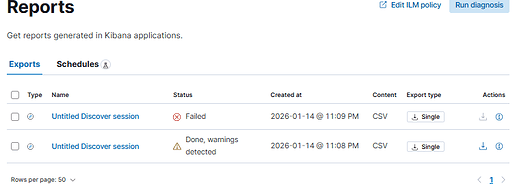
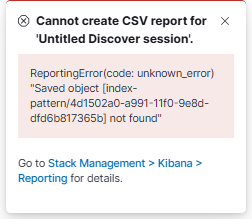
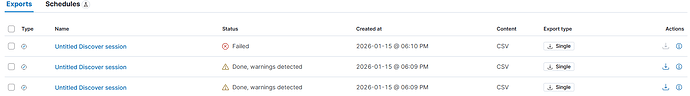
In elasticsearch logs I do see only one message per one attempt [open Discover ~> search query ~> Generate report ~> and again the same (last one Failed suddenly “Processed by admin“ and this time for logs from other “index_pattern/data_view/index“)
[2026-01-15T18:09:29,294][INFO ][t.b.r.a.l.AccessControlListLoggingDecorator] [...] ESC[35mFORBIDDEN by { name: '::Forbid API calls for some specific roles::', policy: FORBID, rules: [ldap_auth, uri_re] req={ ID:XXX#204958833, TYP:GetDataStreamAction$Request, CGR:USER_LDAP_ROLE, USR:XXXUSER, BRS:true, KDX:null, ACT:indices:admin/data_stream/get, OA:HOST_IP/32, XFF:USER_IP, DA:HOST_IP/32, IDX:<N/A>, MET:GET, PTH:/_data_stream/logs, CNT:<N/A>, HDR:x-opaque-id=unknownId, cookie=x-csrf-token-XXX-session_id=XXX; x-csrf-token-XXX=YYY.YYYY, x-ror-kibana-request-method=get, x-ror-kibana-index=.kibana-X, accept=application/vnd.elasticsearch+json; compatible-with=8,text/plain, x-elastic-product-origin=kibana, traceparent=00-X-X-00, tracestate=es=s:0, x-elastic-client-meta=es=8.19.1,js=22.17.1,t=8.9.6,hc=22.17.1, Authorization=<OMITTED>, Host=HOST_IP:HOST_PORT, x-ror-correlation-id=X-X-X-X-X, x-forwarded-for=USER_IP, content-length=0, x-ror-kibana-request-path=/s/default/api/streams/_status, user-agent=Kibana/8.19.7, keep-alive=timeout=10, max=1000, connection=keep-alive, Accept-Charset=utf-8, HIS:[Accept all requests from localhost-> RULES:[hosts->false]], [::XXX0::-> RULES:[auth_key->false]], [::Forbid API calls for some specific roles::-> RULES:[ldap_auth->true, uri_re->true] RESOLVED:[user=XXXUSER;group=LDAP_ROLE;av_groups=XXX_LDAP_ROLES]], }ESC[0m
[2026-01-15T18:09:50,279][INFO ][t.b.r.a.l.AccessControlListLoggingDecorator] [...] ESC[35mFORBIDDEN by { name: '::Forbid API calls for some specific roles::', policy: FORBID, rules: [ldap_auth, uri_re] req={ ID:XXX#204964480, TYP:GetDataStreamAction$Request, CGR:USER_LDAP_ROLE, USR:XXXUSER, BRS:true, KDX:null, ACT:indices:admin/data_stream/get, OA:HOST_IP/32, XFF:USER_IP, DA:HOST_IP/32, IDX:<N/A>, MET:GET, PTH:/_data_stream/logs, CNT:<N/A>, HDR:x-opaque-id=unknownId, cookie=x-csrf-token-XXX-session_id=XXX; x-csrf-token-XXX=YYY.YYYY, traceparent=00-X-X-00, x-ror-kibana-request-method=get, x-ror-kibana-index=.kibana-X, accept=application/vnd.elasticsearch+json; compatible-with=8,text/plain, x-elastic-product-origin=kibana, tracestate=es=s:0, x-elastic-client-meta=es=8.19.1,js=22.17.1,t=8.9.6,hc=22.17.1, Authorization=<OMITTED>, Host=HOST_IP:HOST_PORT, x-ror-correlation-id=X-X-X-X-X, x-forwarded-for=USER_IP, content-length=0, x-ror-kibana-request-path=/s/default/api/streams/_status, user-agent=Kibana/8.19.7, keep-alive=timeout=10, max=1000, connection=keep-alive, Accept-Charset=utf-8, HIS:[Accept all requests from localhost-> RULES:[hosts->false]], [::XXX0::-> RULES:[auth_key->false]], [::Forbid API calls for some specific roles::-> RULES:[ldap_auth->true, uri_re->true] RESOLVED:[user=XXXUSER;group=LDAP_ROLE;av_groups=XXX_LDAP_ROLES]], }ESC[0m
[2026-01-15T18:10:20,244][INFO ][t.b.r.a.l.AccessControlListLoggingDecorator] [...] ESC[35mFORBIDDEN by { name: '::Forbid API calls for some specific roles::', policy: FORBID, rules: [ldap_auth, uri_re] req={ ID:XXX#204985872, TYP:GetDataStreamAction$Request, CGR:USER_LDAP_ROLE, USR:XXXUSER, BRS:true, KDX:null, ACT:indices:admin/data_stream/get, OA:HOST_IP/32, XFF:USER_IP, DA:HOST_IP/32, IDX:<N/A>, MET:GET, PTH:/_data_stream/logs, CNT:<N/A>, HDR:x-opaque-id=unknownId, cookie=x-csrf-token-XXX-session_id=XXX; x-csrf-token-XXX=YYY.YYYY, x-ror-kibana-request-method=get, x-ror-kibana-index=.kibana-X, accept=application/vnd.elasticsearch+json; compatible-with=8,text/plain, traceparent=00-X-X-00, x-elastic-product-origin=kibana, tracestate=es=s:0, x-elastic-client-meta=es=8.19.1,js=22.17.1,t=8.9.6,hc=22.17.1, Authorization=<OMITTED>, Host=HOST_IP:HOST_PORT, x-ror-correlation-id=X-X-X-X-X, x-forwarded-for=USER_IP, content-length=0, x-ror-kibana-request-path=/s/default/api/streams/_status, user-agent=Kibana/8.19.7, keep-alive=timeout=10, max=1000, connection=keep-alive, Accept-Charset=utf-8, HIS:[Accept all requests from localhost-> RULES:[hosts->false]], [::XXX0::-> RULES:[auth_key->false]], [::Forbid API calls for some specific roles::-> RULES:[ldap_auth->true, uri_re->true] RESOLVED:[user=XXXUSER;group=LDAP_ROLE;av_groups=XXX_LDAP_ROLES]], }ESC[0m
“Forbid API calls for some specific roles“ is my rule to restrict LDAP users from using some api actions via “Dev tools“ app and there it works successfully for Kibana 7.17.X and 8.19.X
![]()