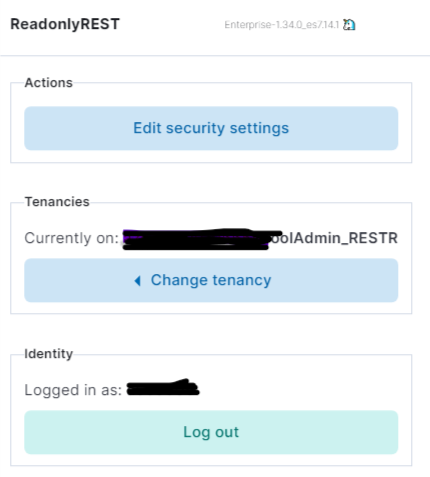
My company is a ReadonlyREST Enterprise subscriber and we are planning to upgrade to Elastic Stack 7.14.1 from 7.6.2
Elastic Version: 7.14.1
ROR Version: readonlyrestkbn@enterprise-1.34.0_es7.14.1
How do I restrict all LDAP users to Edit Security Settings except adminGroup LDAP users?
My readOnlyRest yaml
http.type: ssl_netty4
readonlyrest:
access_control_rules:
- name: "Forbid all LDAP users to delete indices"
type: forbid
actions: ["indices:admin/delete"]
ldap_authentication:
name: "ldap"
cache_ttl_in_sec: 60
- name: "For Observablity Team"
ldap_auth:
name: "ldap"
groups: ["adminGroup"]
cache_ttl_in_sec: 60
- name: "Allow login for LDAP users" #This block will also allow users to create/Modify/Delete visualizations and dashboards
ldap_authentication:
name: "ldap"
cache_ttl_in_sec: 60
indices: [".kibana"]
kibana_hide_apps: [ "Security", "Management|Stack Management", "Enterprise Search", "Observability" , "Home", "Integrations"]
- name: "Forbid below indices for LDAP users"
type: forbid
indices: ["readonlyrest*"]
ldap_authentication:
name: "ldap"
cache_ttl_in_sec: 60
- name: "Allow access to all indices for LDAP users"
kibana_access: ro
ldap_authentication:
name: "ldap"
cache_ttl_in_sec: 60
- name: "::LOGSTASH::"
auth_key: logstash:logstash
actions: ["cluster:monitor/main","indices:admin/types/exists","indices:data/read/*","indices:data/write/*","indices:admin/template/*","indices:admin/create"]
verbosity: error
- name: "::KIBANA-SRV::"
auth_key: kibana:K16@n@!
verbosity: error
ssl:
enable: true
keystore_file: "keystore.jks"
keystore_pass: xxxxx
key_alias: appcertificate
key_pass: xxxxx
audit_collector: true
audit_serializer: tech.beshu.ror.requestcontext.QueryAuditLogSerializer
audit_index_template: "'readonlyrest_audit'-yyyy-MM"
prompt_for_basic_auth: true
response_if_req_forbidden: "This action is forbidden. Contact Observablity team for access "
ldaps:
- name: .....