ror_1.16.16
kbn_ent_1.16.16
ELK 6.2.2
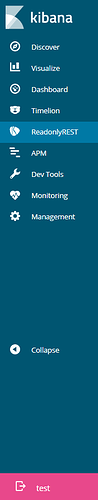
I log into Kibana and both users use the default .kibana-6 index, I do not see a tenancy dropdown button, and all of the apps that are configured to hide are still shown. Not sure if I am missing something obvious or not.
For example:
- Logging in as test:test you can see the ReadonlyREST app but will get permission denied when going into it
- Logging in as testadm:testadm ReadonlyREST app works properly
- Both users are presented with the same list of Kibana apps.
readonlyrest:
response_if_req_forbidden: Forbidden by ReadonlyREST ES plugin
prompt_for_basic_auth: false
audit_collector: true
access_control_rules:
#########################################################
# Allow Kibana monitoring to work
#########################################################
- name: "::Kibana XPack Monitoring::"
type: allow
actions: ["cluster:monitor/*","cluster:admin/xpack/*","indices:data/read/*","indices:data/write/*","indices:admin/*"]
indices: [".kibana*",".monitoring*"]
hosts: ["127.0.0.1"]
verbosity: error
#####################################################################################
# These credentials have no limitations, and shall be used only by the Kibana daemon.
#####################################################################################
- name: "::KIBANA::"
type: allow
auth_key: kibana:readonlyrest
verbosity: error
#####################################################################################
# Local Groups
#####################################################################################
- name: "::Personal::RW::Local"
type: allow
groups: ["kibana-personal"]
kibana_access: rw
kibana_hide_apps: ["readonlyrest_kbn", "timelion", "kibana:dev_tools", "kibana:monitoring", "kibana:management"]
kibana_index: ".kibana_@{user}"
actions: ["indices:data/read/*"]
- name: "::Admin::Local"
type: allow
groups: ["kibana-admin"]
kibana_access: admin
indices: ["*"]
actions: ["indices:data/read/*","cluster:admin/rradmin/"]
- name: "::InfoSec::RO::Local"
type: allow
groups: ["kibana-ro-infosec"]
kibana_access: ro
kibana_hide_apps: ["readonlyrest_kbn", "timelion", "kibana:dev_tools", "kibana:monitoring", "kibana:management"]
kibana_index: ".kibana_infosec"
actions: ["indices:data/read/*"]
indices: ["infosec*","firewall*"]
- name: "::InfoSec::RW::Local"
type: allow
groups: ["kibana-rw-infosec"]
kibana_access: rw
kibana_hide_apps: ["readonlyrest_kbn", "timelion", "kibana:dev_tools", "kibana:monitoring"]
kibana_index: ".kibana_infosec"
actions: ["indices:data/read/*"]
indices: ["infosec*","firewall*"]
#####################################################################################
# Local Users
#####################################################################################
users:
- username: testadm
auth_key: testadm:testadm
groups: ["kibana-personal", "kibana-admin", "kibana-rw-infosec"]
- username: test
auth_key: test:test
groups: ["kibana-personal", "kibana-ro-infosec"]