I now tried a few different approaches, but no luck so far.
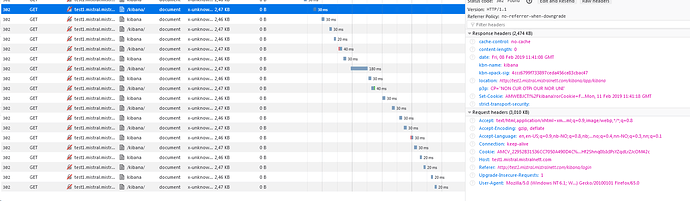
One approach was I tried just adding kibana_index to the blocks, but then I get stuck in an infinate redirect loop when loading kibana.
The config:
readonlyrest:
access_control_rules:
- name: "::KIBANA-SRV::"
auth_key: kibana:kibana
verbosity: error
- name: adminuser
kibana_access: admin
kibana_index: .kibana_teama
indices: [ ".kibana_teama"]
jwt_auth:
name: "webseal"
roles: ["kibana_admin"]
- name: readwrite
kibana_access: admin
kibana_index: .kibana_teamb
indices: [ ".kibana_teamb"]
jwt_auth:
name: "webseal"
roles: ["kibana_user"]
jwt:
- name: webseal
signature_algo: RSA
signature_key: "****************"
user_claim: sub
roles_claim: groups
header_name: jwt
Log line that is repeated over and over again when trying to use kibana:
[2019-02-08T12:24:52,360][INFO ][t.b.r.a.ACL ] [NpgnpOt] ALLOWED by { name: 'adminuser', policy: ALLOW, rules: [kibana_access, kibana_index, indices, jwt_auth]} req={ ID:891669212-1216594734#26999, TYP:GetRequest, CGR:N/A, USR:G019496, BRS:false, KDX:.kibana_teama, ACT:indices:data/read/get, OA:127.0.0.1, DA:127.0.0.1, IDX:.kibana_teama, MET:GET, PTH:/.kibana_teama/doc/space%3Adefault, CNT:<N/A>, HDR:{Connection=keep-alive, Host=localhost:9200, Content-Length=0, jwt=eyJraWQiOiJkTmZscXUtU2pyLUgzbVZsU0IwSHIwSHFTQ3dhSFN0cHRxd2RyYTdqRk8wIiwiYWxnIjoiUlMyNTYifQ.eyJzdWIiOiJHMDE5NDk2IiwiaXNzIjoiaHR0cHM6Ly93d3cuZ2plbnNpZGlnZS5ubyIsImF1ZCI6InVybjpsaWJlcnR5IiwiaWF0IjoxNTQ5NjI1MjU5LCJleHAiOjE1NDk2Mjg4NTksInNlc3MiOiI5ZDlkMWJhNC0yYjdiLTExZTktYTkyYy0wMDUwNTY4MjZlZDgiLCJncm91cHMiOlsia2liYW5hX3VzZXIiLCJraWJhbmFfYWRtaW4iXX0.OgXr0ba6PksZa1J1akISfR3x2QjJisYQ13s-JeQT2hxcZo7grl-U3oHqDQ_UzGRsdr6Fn2pXbS6J48EN1FAzKRfjuSmF1q0A_u2Pt2dDNimtfbgs92xbccR6AwrcCLjHwHBx6P-Xlfa7EhYTBafCMLVCKHDH9H77S6UUMMV2Vp3VKfwzNEC0R0WRIJACw4lXel4t_eHj7GjNnOYyD_lHXunCBiaNdeEAA93TPeBvQhP8KXZWKhqQxy68c6mso_RMjeVkqe2X63n159hue9aVrVECkcZRXpQ1OQwMgHIC1aKu8te3kt2OQS2wHvmeq8UQDWLy8iqJRSYoWmb8AEnduDDOwyTaXDlr_HxslA0P_2iDn2ABxrKjXiq93WehtaGmiVseehhl1onyuhqzwJjRpXCC3uXav_3exaj6XTWu7naTEFEqqyG8euKmbyBYRZaeIn7et5Uf45qhcUpi96hCppmYbsbWGUt0AlzC0v0okUWqJtlOgA3do1aiQDcDmkP64yFDnUM5bHpzdWrQ1ko5EVekyrqERAUlKfwo4_Hx4bmUjWV4QEWc2WXDVC5z9olNjwTRU31ij72uzQEnQ87eWGFIi7tQiVBf2ThzFNfS1HWfzz5y6sjcRNr3E4K1kIQNVg941QXpDf5YJo7bAwPKr4ryoIyUBjkC992PN1wJQU0}, HIS:[::KIBANA-SRV::->[auth_key->false]], [adminuser->[kibana_access->true, indices->true, jwt_auth->true, kibana_index->true]] }
[2019-02-08T12:24:52,388][INFO ][t.b.r.a.ACL ] [NpgnpOt] ALLOWED by { name: 'adminuser', policy: ALLOW, rules: [kibana_access, kibana_index, indices, jwt_auth]} req={ ID:1718188808--350773647#27001, TYP:SearchRequest, CGR:N/A, USR:G019496, BRS:false, KDX:.kibana_teama, ACT:indices:data/read/search, OA:127.0.0.1, DA:127.0.0.1, IDX:.kibana_teama, MET:POST, PTH:/.kibana_teama/_search?size=1000&from=0, CNT:<OMITTED, LENGTH=245>, HDR:{Connection=keep-alive, content-type=application/json, Host=localhost:9200, Content-Length=245, jwt=eyJraWQiOiJkTmZscXUtU2pyLUgzbVZsU0IwSHIwSHFTQ3dhSFN0cHRxd2RyYTdqRk8wIiwiYWxnIjoiUlMyNTYifQ.eyJzdWIiOiJHMDE5NDk2IiwiaXNzIjoiaHR0cHM6Ly93d3cuZ2plbnNpZGlnZS5ubyIsImF1ZCI6InVybjpsaWJlcnR5IiwiaWF0IjoxNTQ5NjI1MjU5LCJleHAiOjE1NDk2Mjg4NTksInNlc3MiOiI5ZDlkMWJhNC0yYjdiLTExZTktYTkyYy0wMDUwNTY4MjZlZDgiLCJncm91cHMiOlsia2liYW5hX3VzZXIiLCJraWJhbmFfYWRtaW4iXX0.OgXr0ba6PksZa1J1akISfR3x2QjJisYQ13s-JeQT2hxcZo7grl-U3oHqDQ_UzGRsdr6Fn2pXbS6J48EN1FAzKRfjuSmF1q0A_u2Pt2dDNimtfbgs92xbccR6AwrcCLjHwHBx6P-Xlfa7EhYTBafCMLVCKHDH9H77S6UUMMV2Vp3VKfwzNEC0R0WRIJACw4lXel4t_eHj7GjNnOYyD_lHXunCBiaNdeEAA93TPeBvQhP8KXZWKhqQxy68c6mso_RMjeVkqe2X63n159hue9aVrVECkcZRXpQ1OQwMgHIC1aKu8te3kt2OQS2wHvmeq8UQDWLy8iqJRSYoWmb8AEnduDDOwyTaXDlr_HxslA0P_2iDn2ABxrKjXiq93WehtaGmiVseehhl1onyuhqzwJjRpXCC3uXav_3exaj6XTWu7naTEFEqqyG8euKmbyBYRZaeIn7et5Uf45qhcUpi96hCppmYbsbWGUt0AlzC0v0okUWqJtlOgA3do1aiQDcDmkP64yFDnUM5bHpzdWrQ1ko5EVekyrqERAUlKfwo4_Hx4bmUjWV4QEWc2WXDVC5z9olNjwTRU31ij72uzQEnQ87eWGFIi7tQiVBf2ThzFNfS1HWfzz5y6sjcRNr3E4K1kIQNVg941QXpDf5YJo7bAwPKr4ryoIyUBjkC992PN1wJQU0}, HIS:[::KIBANA-SRV::->[auth_key->false]], [adminuser->[kibana_access->true, indices->true, jwt_auth->true, kibana_index->true]] }
[2019-02-08T12:24:52,429][INFO ][t.b.r.a.ACL ] [NpgnpOt] ALLOWED by { name: 'adminuser', policy: ALLOW, rules: [kibana_access, kibana_index, indices, jwt_auth]} req={ ID:23137856-436819866#27003, TYP:GetRequest, CGR:N/A, USR:G019496, BRS:false, KDX:.kibana_teama, ACT:indices:data/read/get, OA:127.0.0.1, DA:127.0.0.1, IDX:.kibana_teama, MET:GET, PTH:/.kibana_teama/doc/space%3Adefault, CNT:<N/A>, HDR:{Connection=keep-alive, Host=localhost:9200, Content-Length=0, jwt=eyJraWQiOiJkTmZscXUtU2pyLUgzbVZsU0IwSHIwSHFTQ3dhSFN0cHRxd2RyYTdqRk8wIiwiYWxnIjoiUlMyNTYifQ.eyJzdWIiOiJHMDE5NDk2IiwiaXNzIjoiaHR0cHM6Ly93d3cuZ2plbnNpZGlnZS5ubyIsImF1ZCI6InVybjpsaWJlcnR5IiwiaWF0IjoxNTQ5NjI1MjU5LCJleHAiOjE1NDk2Mjg4NTksInNlc3MiOiI5ZDlkMWJhNC0yYjdiLTExZTktYTkyYy0wMDUwNTY4MjZlZDgiLCJncm91cHMiOlsia2liYW5hX3VzZXIiLCJraWJhbmFfYWRtaW4iXX0.OgXr0ba6PksZa1J1akISfR3x2QjJisYQ13s-JeQT2hxcZo7grl-U3oHqDQ_UzGRsdr6Fn2pXbS6J48EN1FAzKRfjuSmF1q0A_u2Pt2dDNimtfbgs92xbccR6AwrcCLjHwHBx6P-Xlfa7EhYTBafCMLVCKHDH9H77S6UUMMV2Vp3VKfwzNEC0R0WRIJACw4lXel4t_eHj7GjNnOYyD_lHXunCBiaNdeEAA93TPeBvQhP8KXZWKhqQxy68c6mso_RMjeVkqe2X63n159hue9aVrVECkcZRXpQ1OQwMgHIC1aKu8te3kt2OQS2wHvmeq8UQDWLy8iqJRSYoWmb8AEnduDDOwyTaXDlr_HxslA0P_2iDn2ABxrKjXiq93WehtaGmiVseehhl1onyuhqzwJjRpXCC3uXav_3exaj6XTWu7naTEFEqqyG8euKmbyBYRZaeIn7et5Uf45qhcUpi96hCppmYbsbWGUt0AlzC0v0okUWqJtlOgA3do1aiQDcDmkP64yFDnUM5bHpzdWrQ1ko5EVekyrqERAUlKfwo4_Hx4bmUjWV4QEWc2WXDVC5z9olNjwTRU31ij72uzQEnQ87eWGFIi7tQiVBf2ThzFNfS1HWfzz5y6sjcRNr3E4K1kIQNVg941QXpDf5YJo7bAwPKr4ryoIyUBjkC992PN1wJQU0}, HIS:[::KIBANA-SRV::->[auth_key->false]], [adminuser->[kibana_access->true, indices->true, jwt_auth->true, kibana_index->true]] }
[2019-02-08T12:24:52,464][INFO ][t.b.r.a.ACL ] [NpgnpOt] ALLOWED by { name: 'adminuser', policy: ALLOW, rules: [kibana_access, kibana_index, indices, jwt_auth]} req={ ID:1279622470--350773647#27005, TYP:SearchRequest, CGR:N/A, USR:G019496, BRS:false, KDX:.kibana_teama, ACT:indices:data/read/search, OA:127.0.0.1, DA:127.0.0.1, IDX:.kibana_teama, MET:POST, PTH:/.kibana_teama/_search?size=1000&from=0, CNT:<OMITTED, LENGTH=245>, HDR:{Connection=keep-alive, content-type=application/json, Host=localhost:9200, Content-Length=245, jwt=eyJraWQiOiJkTmZscXUtU2pyLUgzbVZsU0IwSHIwSHFTQ3dhSFN0cHRxd2RyYTdqRk8wIiwiYWxnIjoiUlMyNTYifQ.eyJzdWIiOiJHMDE5NDk2IiwiaXNzIjoiaHR0cHM6Ly93d3cuZ2plbnNpZGlnZS5ubyIsImF1ZCI6InVybjpsaWJlcnR5IiwiaWF0IjoxNTQ5NjI1MjU5LCJleHAiOjE1NDk2Mjg4NTksInNlc3MiOiI5ZDlkMWJhNC0yYjdiLTExZTktYTkyYy0wMDUwNTY4MjZlZDgiLCJncm91cHMiOlsia2liYW5hX3VzZXIiLCJraWJhbmFfYWRtaW4iXX0.OgXr0ba6PksZa1J1akISfR3x2QjJisYQ13s-JeQT2hxcZo7grl-U3oHqDQ_UzGRsdr6Fn2pXbS6J48EN1FAzKRfjuSmF1q0A_u2Pt2dDNimtfbgs92xbccR6AwrcCLjHwHBx6P-Xlfa7EhYTBafCMLVCKHDH9H77S6UUMMV2Vp3VKfwzNEC0R0WRIJACw4lXel4t_eHj7GjNnOYyD_lHXunCBiaNdeEAA93TPeBvQhP8KXZWKhqQxy68c6mso_RMjeVkqe2X63n159hue9aVrVECkcZRXpQ1OQwMgHIC1aKu8te3kt2OQS2wHvmeq8UQDWLy8iqJRSYoWmb8AEnduDDOwyTaXDlr_HxslA0P_2iDn2ABxrKjXiq93WehtaGmiVseehhl1onyuhqzwJjRpXCC3uXav_3exaj6XTWu7naTEFEqqyG8euKmbyBYRZaeIn7et5Uf45qhcUpi96hCppmYbsbWGUt0AlzC0v0okUWqJtlOgA3do1aiQDcDmkP64yFDnUM5bHpzdWrQ1ko5EVekyrqERAUlKfwo4_Hx4bmUjWV4QEWc2WXDVC5z9olNjwTRU31ij72uzQEnQ87eWGFIi7tQiVBf2ThzFNfS1HWfzz5y6sjcRNr3E4K1kIQNVg941QXpDf5YJo7bAwPKr4ryoIyUBjkC992PN1wJQU0}, HIS:[::KIBANA-SRV::->[auth_key->false]], [adminuser->[kibana_access->true, indices->true, jwt_auth->true, kibana_index->true]] }
@sscarduzio : Could you have a look at this and see what I am doing wrong?