Ok so,
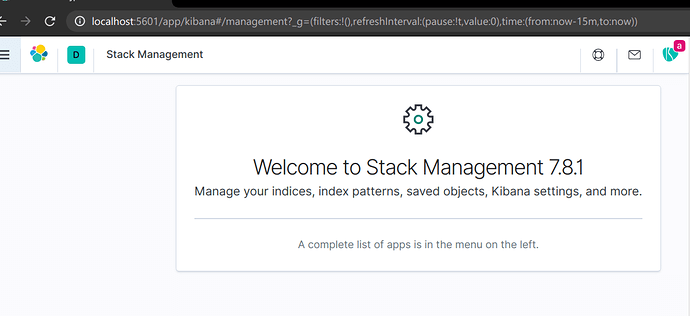
There is my access block that was resolved as ALLOWED (as you can see there is kibana:management):
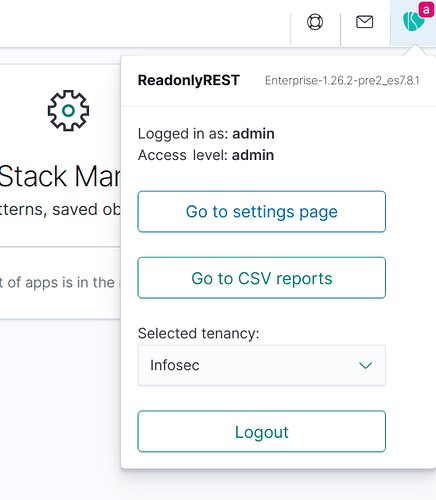
Aswell the readonlyrest_kbn is not hidden
- name: "Proxy - dna - Kibana"
type: allow
uri_re: ["^/dna.*","^/.kibana.*","^/_mapping","^/_aliases","^/_template","^/_cat.*","^/_count.*","^/_search/scroll","^/_msearch", "^/_mget", "^/_readonlyrest"]
headers: ["XXXX:XXXXX"]
proxy_auth:
proxy_auth_config: "proxy1"
users: ["*"]
ldap_authorization:
name: "ldap1"
groups: ["CHR-GP-SV-INL-D-ElasticserviceDna-Dev", "CHR-GP-SV-DNA-P-USER-Dev", "CHR-GP-SV-DNA-P-ADMIN-Dev"]
indices: [".kibana*"]
kibana_hide_apps: [ "timelion","logs","metrics","canvas","maps", "code", "ml", "infra:home", "infra:logs", "apm", "uptime", "siem", "graph", "monitoring", "kibana:management", "readonlyrest_kbn" ]
actions: ["indices:data/read/*","indices:data/write/*", "indices:admin/mappings/get", "indices:admin/template/get", "indices:admin/get", "cluster:monitor/state", "indices:admin/aliases/get", "indices:data/read/mget", "cluster:ror/user_metadata/get"]
There is log in that regards, i trimmed the logs because otherwise it will be too big, because of too many ACL blocks we have:
[2021-02-16T15:10:09,347][INFO ][tech.beshu.ror.accesscontrol.logging.AccessControlLoggingDecorator] [elasticsearch-client-01] e[36mALLOWED by { name: 'Proxy - dna - Kibana', policy: ALLOW, rules: [proxy_auth,ldap_authorization,uri_re,headers_and,actions,indices,kibana_hide_apps] req={ ID:1491628833-148778721#10272, TYP:RRUserMetadataRequest, CGR:CHR-GP-SV-INL-D-ElasticserviceDna-Dev, USR:XXXX, BRS:false, KDX:null, ACT:cluster:ror/user_metadata/get, OA:XXXX, XFF:null, DA:XXXX, IDX:<N/A>, MET:GET, PTH:/_readonlyrest/metadata/current_user, CNT:<N/A>, HDR:Authorization=<OMITTED>, Connection=keep-alive, Content-Length=0, Host=dev-ire-elasticsearch.swissre.com:9200, x-auth-key=<OMITTED>, x-forwarded-user=XXXX, x-ror-current-group=CHR-GP-SV-INL-D-ElasticserviceDna-Dev, x-ror-kibana-request-method=get, x-ror-kibana-request-path=/switch-group, HIS:[... [Proxy - dna - Kibana-> RULES:[proxy_auth->true, ldap_authorization->true, uri_re->true, headers_and->true, actions->true, indices->true, kibana_hide_apps->true] RESOLVED:[user=XXXX;group=CHR-GP-SV-INL-D-ElasticserviceDna-Dev;av_groups=CHR-GP-SV-INL-D-ElasticserviceTreatyPC-Dev,CHR-GP-SV-DNA-P-USER-Dev,CHR-GP-SV-INL-D-ElasticserviceDna-Dev,CHR-GP-SV-INL-D-ElasticserviceTreatyLH-Dev,CHR-GP-SV-INL-D-ElasticserviceTreaty-Dev,CHR-GP-SV-INL-D-Elasticservice-Dev,CHR-GP-SV-INL-D-ElasticserviceBmpf-Dev]] ... }e[0m
And there is crazy logs when i enabled audit till i deleted the index manually:
2021.02.15 13:47:13.903 -
[2021-02-15T14:47:09,572][INFO ][o.e.c.m.MetaDataDeleteIndexService] [elasticsearch-master-01] [readonlyrest_audit-2021-02-15/x9THhGLrQFGAzB6D4PC9DA] deleting index
2021.02.15 13:46:13.831 -
at io.netty.util.internal.ThreadExecutorMap$2.run(ThreadExecutorMap.java:74) [netty-common-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.util.concurrent.SingleThreadEventExecutor$4.run(SingleThreadEventExecutor.java:989) [netty-common-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.nio.NioEventLoop.processSelectedKey(NioEventLoop.java:714) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.DefaultChannelPipeline$HeadContext.channelRead(DefaultChannelPipeline.java:1410) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.handler.codec.ByteToMessageDecoder.channelRead(ByteToMessageDecoder.java:276) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at java.lang.Thread.run(Thread.java:834) [?:?]
2021.02.15 13:46:13.831 -
at io.netty.channel.nio.NioEventLoop.run(NioEventLoop.java:493) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.nio.NioEventLoop.processSelectedKeysPlain(NioEventLoop.java:615) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.nio.NioEventLoop.processSelectedKeys(NioEventLoop.java:578) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.handler.codec.ByteToMessageDecoder.callDecode(ByteToMessageDecoder.java:440) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.nio.AbstractNioByteChannel$NioByteUnsafe.read(AbstractNioByteChannel.java:166) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.DefaultChannelPipeline.fireChannelRead(DefaultChannelPipeline.java:919) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.handler.codec.ByteToMessageDecoder.decodeRemovalReentryProtection(ByteToMessageDecoder.java:501) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.831 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.timeout.IdleStateHandler.channelRead(IdleStateHandler.java:286) [netty-handler-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.MessageToMessageDecoder.channelRead(MessageToMessageDecoder.java:103) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at org.elasticsearch.rest.RestController.dispatchRequest(RestController.java:176) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.client.support.AbstractClient.get(AbstractClient.java:497) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.client.node.NodeClient.executeLocally(NodeClient.java:83) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.action.support.TransportAction.execute(TransportAction.java:64) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.action.support.TransportAction.execute(TransportAction.java:129) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at scala.runtime.java8.JFunction0$mcV$sp.apply(JFunction0$mcV$sp.java:23) [scala-library-2.12.10.jar:?]
2021.02.15 13:46:13.830 -
at monix.eval.Task.runAsync(Task.scala:659) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.commitResult(RegularRequestHandler.scala:64) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.MessageToMessageDecoder.channelRead(MessageToMessageDecoder.java:103) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.MessageToMessageDecoder.channelRead(MessageToMessageDecoder.java:103) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.MessageToMessageCodec.channelRead(MessageToMessageCodec.java:111) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.netty4.Netty4HttpRequestHandler.channelRead0(Netty4HttpRequestHandler.java:54) [transport-netty4-client-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.AbstractHttpServerTransport.dispatchRequest(AbstractHttpServerTransport.java:329) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.rest.RestController.dispatchRequest(RestController.java:236) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.rest.BaseRestHandler.handleRequest(BaseRestHandler.java:115) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.client.support.AbstractClient.execute(AbstractClient.java:399) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.action.support.TransportAction$RequestFilterChain.proceed(TransportAction.java:151) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.IndexLevelActionFilter.apply(IndexLevelActionFilter.scala:82) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at java.security.AccessController.doPrivileged(Native Method) [?:?]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.IndexLevelActionFilter.$anonfun$apply$1(IndexLevelActionFilter.scala:101) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at monix.eval.Task$Map.apply(Task.scala:4510) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at monix.eval.Task$Map.apply(Task.scala:4514) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.$anonfun$handle$1$adapted(RegularRequestHandler.scala:54) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.$anonfun$handle$2(RegularRequestHandler.scala:56) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.ByteToMessageDecoder.fireChannelRead(ByteToMessageDecoder.java:324) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.netty4.Netty4HttpRequestHandler.channelRead0(Netty4HttpRequestHandler.java:29) [transport-netty4-client-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.ReadonlyRestPlugin.$anonfun$getRestHandlerWrapper$2(ReadonlyRestPlugin.scala:219) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at org.elasticsearch.client.node.NodeClient.doExecute(NodeClient.java:72) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.IndexLevelActionFilter.handleRequest(IndexLevelActionFilter.scala:127) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.$anonfun$handle$1(RegularRequestHandler.scala:55) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.utils.ScalaOps$AutoCloseableOps$.bracket$extension(ScalaOps.scala:155) [core-1.26.1.jar:?]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.$anonfun$handle$2$adapted(RegularRequestHandler.scala:55) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.830 -
at io.netty.handler.ssl.SslHandler.unwrap(SslHandler.java:1533) [netty-handler-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.codec.ByteToMessageDecoder.channelRead(ByteToMessageDecoder.java:296) [netty-codec-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:365) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.netty4.Netty4HttpPipeliningHandler.channelRead(Netty4HttpPipeliningHandler.java:58) [transport-netty4-client-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.rest.RestController.tryAllHandlers(RestController.java:318) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.utils.AccessControllerHelper$$anon$1.run(AccessControllerHelper.scala:25) [core-1.26.1.jar:?]
2021.02.15 13:46:13.830 -
at monix.eval.Task.runAsyncOpt(Task.scala:709) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at monix.eval.Task.runAsyncOptF(Task.scala:811) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at monix.eval.internal.TaskRunLoop$.startLight(TaskRunLoop.scala:331) [monix-eval_2.12-3.0.0.jar:3.0.0]
2021.02.15 13:46:13.830 -
at io.netty.handler.ssl.SslHandler.decode(SslHandler.java:1329) [netty-handler-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.handler.ssl.SslHandler.decodeJdkCompatible(SslHandler.java:1282) [netty-handler-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.fireChannelRead(AbstractChannelHandlerContext.java:357) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.AbstractChannelHandlerContext.invokeChannelRead(AbstractChannelHandlerContext.java:379) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at io.netty.channel.SimpleChannelInboundHandler.channelRead(SimpleChannelInboundHandler.java:99) [netty-transport-4.1.53.Final.jar:4.1.53.Final]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.AbstractHttpServerTransport.incomingRequest(AbstractHttpServerTransport.java:308) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.http.AbstractHttpServerTransport.handleIncomingRequest(AbstractHttpServerTransport.java:383) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at org.elasticsearch.rest.action.document.RestGetAction.lambda$prepareRequest$0(RestGetAction.java:98) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.830 -
at tech.beshu.ror.utils.AccessControllerHelper$.doPrivileged(AccessControllerHelper.scala:24) [core-1.26.1.jar:?]
2021.02.15 13:46:13.830 -
at scala.util.Try$.apply(Try.scala:213) [scala-library-2.12.10.jar:?]
2021.02.15 13:46:13.829 -
at org.elasticsearch.action.support.single.shard.TransportSingleShardAction.doExecute(TransportSingleShardAction.java:62) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.829 -
at org.elasticsearch.action.support.single.shard.TransportSingleShardAction$AsyncSingleAction.start(TransportSingleShardAction.java:201) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.829 -
at org.elasticsearch.action.support.single.shard.TransportSingleShardAction$AsyncSingleAction.perform(TransportSingleShardAction.java:224) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.829 -
at org.elasticsearch.action.support.TransportAction$RequestFilterChain.proceed(TransportAction.java:153) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.829 -
at org.elasticsearch.action.support.single.shard.TransportSingleShardAction.doExecute(TransportSingleShardAction.java:103) [elasticsearch-7.7.1.jar:7.7.1]
2021.02.15 13:46:13.829 -
org.elasticsearch.action.NoShardAvailableActionException: No shard available for [get [.kibana][_doc][space:default]: routing [null]]
2021.02.15 13:46:13.829 -
at scala.runtime.java8.JFunction0$mcV$sp.apply(JFunction0$mcV$sp.java:23) [scala-library-2.12.10.jar:?]
2021.02.15 13:46:13.829 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.$anonfun$commitResult$1(RegularRequestHandler.scala:66) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.829 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.proceed(RegularRequestHandler.scala:195) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:13.829 -
[2021-02-15T14:46:12,436][WARN ][r.suppressed ] [elasticsearch-client-01] path: /.kibana/_doc/space%3Adefault, params: {index=.kibana, id=space:default}
2021.02.15 13:46:13.829 -
at tech.beshu.ror.es.request.handler.RegularRequestHandler.onAllow(RegularRequestHandler.scala:102) [readonlyrest-1.26.1_es7.7.1.jar:?]
2021.02.15 13:46:12.273 -
[2021-02-15T14:46:10,951][INFO ][t.b.r.b.RorInstance ] [elasticsearch-data-04] ReadonlyREST core was loaded ...